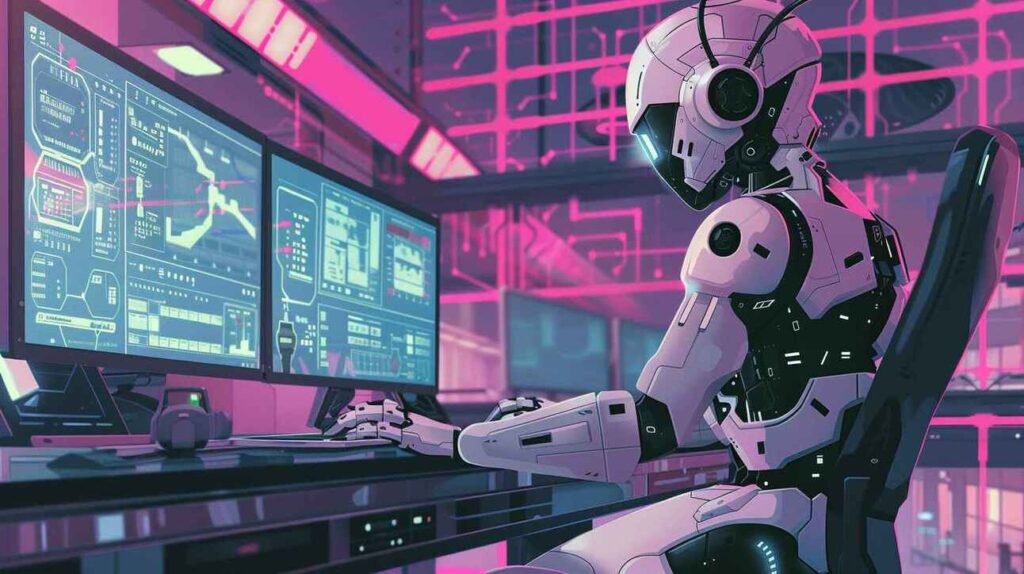
Web Application Security Scan. Discover. Fix.
With Cybervolt, all it takes is connecting your DNS to our scanning engine, our platform handles everything else automatically. Our OWASP website vulnerability scanner delivers banking-grade TLS compliance checks aligned with PCI-DSS, FIPS, and NIST standards. Built with enterprise-level detection logic, with payload simulations to test all attack surface
( 24 k+ Positive Reviews )







Why Choose CyberVolt?
Our platform delivers PCI-DSS–aligned TLS validation, DAST testing, and OWASP compliance checks using banking-grade cryptographic assessment mapped to FIPS and NIST standards.
Unlike generic scanners, Cybervolt applies enterprise-grade detection logic
LIGHT SCAN [100 USD]
Non-intrusive passive security scanning, with no payload simulations. primarily to test PCI-DSS TLS COMPLIANCE

PREMIUM SCAN [300 USD]
Complete application assessment, total property discovery of all attack surface including domains and sub domains within the organization, API testing, Intrusive deep scanning, payload simulation exploitation scanning, OWASP scanning , e.t.c
FOR TECHNOLOGY COMPANIES
Assisting technology companies from development to production, securing digital infrastructure, Our scanning engines detect vulnerabilities within minutes, in events of technology updates or audits, making sure all assets are properly checked for vulnerabilities

For business corporations and others
Complete application assessment, total property discovery of all attack surface including domains and sub domains within the organization, securing them through premium testing services
What Is Web Application Security?
Web application security is the practice of protecting websites, applications, and APIs from attacks. It’s a broad field, but its core purpose is to ensure that web applications operate reliably while defending the business against cyber vandalism, data theft, unethical competition, and other harmful consequences.
Because the Internet is global, web applications and APIs are exposed to threats from anywhere in the world. These threats vary in scale and complexity, so web application security includes a range of strategies that span the entire software supply chain.
Building a secured tommorrow .
What Is Credential Stuffing?
Credential stuffing is one of the most common and dangerous forms of cyberattacks today. If you’ve ever reused a password across multiple accounts
Buffer Overflow: Unlocking the Secrets to Secure Software Development
Buffer overflow is one of the most notorious vulnerabilities in the world of cybersecurity, and it has been responsible for many high-profile security breaches.
What Are Zero-Day Vulnerabilities? Everything You Need to Know
In today’s fast-paced cybersecurity landscape, zero-day vulnerabilities are some of the most dangerous threats organizations face. These flaws are exploited before developers even know they exist—making them incredibly hard to detect and defend against.
API Scanning
Deliver continuous, high-precision API security assessments that adapt in real time providing clear, actionable findings you can trust.
Experience a new standard of dynamic API scanning, powered by proprietary, research-driven testing methodologies.
Gain complete, unified visibility across all your APIs, enabling confident security decisions and reduced risk exposure.
Our satisfied custumers





Google Reviews
Very Insightful.
Your Trusted Partner in Cybersecurity
Equiping companies, organizations, and governments with cutting edge cybersecurity services
- Penetration Testing (Web, Mobile, Network, Cloud, API)
- PCI DSS compliance
- Red Teaming & Phishing Simulation
- Security Consulting & Remediation Guidance
- NIST Framework
- Vulnerability Assessments
- Security Audits & Compliance Support
Latest Blog & Articles
Get the latest cyber security research articles and news
Public Key Infrastructure (PKI)
Prompt Engineering
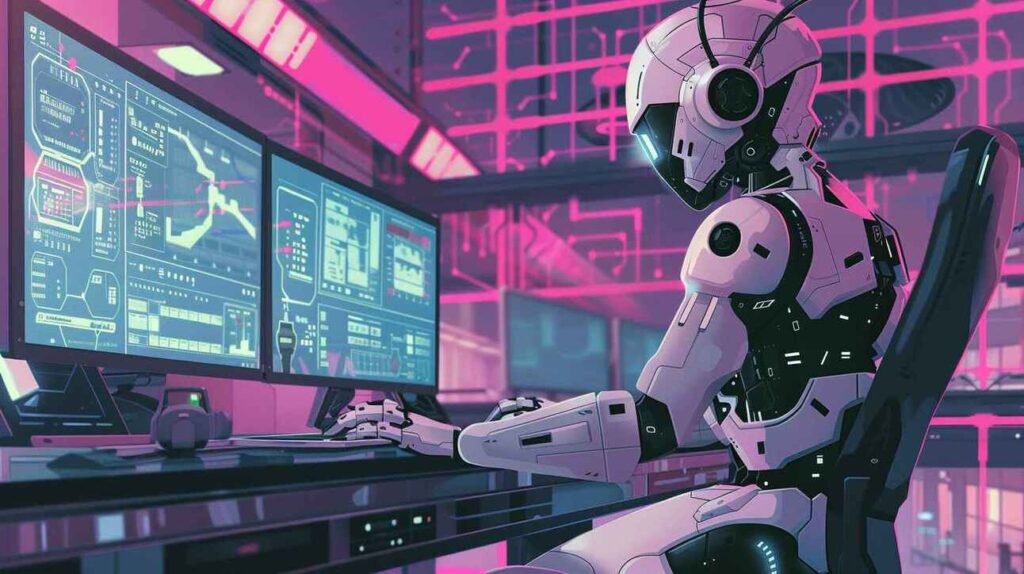
Stay Ahead with cybervault Intelligence
Gain the advantage with our cybervault research team. Cybervolt continuously integrates research from its global community of vetted ethical hackers, giving you access to the latest security discoveries often within minutes. This means emerging, undocumented vulnerabilities are identified and tested against your environment faster, helping you stay protected as threats evolve.
Building a secured tommorrow .
(OWASP top 10) Web Application attack simulations
The OWASP Top 10 is a globally recognized list of the most critical web application security risks, maintained by the Open Web Application Security Project (OWASP). It’s widely used by developers, security teams, and organizations as a baseline for building and assessing secure applications.
DAST - Dynamic Application Security Testing.
It’s a security testing approach that finds vulnerabilities in an application while it’s running, by interacting with it the same way an attacker would.
PCI DSS - Payment Card Industry Data Security Standard.
It is a global security standard designed to protect credit and debit card data and reduce fraud across payment systems.
NIST - National Institute of Standards and Technology.
widely trusted cybersecurity standards and frameworks used by organizations around the world to manage and reduce security risk.
NIST provides practical guidance on how to:
Protect systems and data.
Identify and manage cyber risks.
Detect and respond to security incidents.
Recover from attacks
